Is your online identity secure?
Is your online identity secure?
Are you concerned about hackers?
To discover how to secure your social profiles, your online accounts and your identity from hackers, I interview Chalene Johnson and Darren Natoni.
More About This Show
The Social Media Marketing podcast is an on-demand talk radio show from Social Media Examiner. It's designed to help busy marketers and business owners discover what works with social media marketing.
In this episode I interview Chalene Johnson and Darren Natoni. Chalene is a fitness celebrity, author of the book Push and has large followings on Instagram and Facebook. She's also someone whose online identity was hijacked and sold to the highest bidder. Darren is a former special agent with the DEA who specializes in online security. He's also the chief technology officer for Shaun T, a fitness celebrity with millions of followers.
Chalene and Darren will explore what marketers and entrepreneurs need to know when it comes to securing their online accounts and more.
You'll discover how to be safe online and protect your identity from hackers.

Share your feedback, read the show notes and get the links mentioned in this episode below.
Listen Now
Where to subscribe: Apple Podcasts | Spotify | YouTube Music | YouTube | Amazon Music | RSS
Here are some of the things you'll discover in this show:
Online Security for Business
When Chalene got hacked
Chalene explains how she was enjoying a perfect day (a fact that she even tweeted out), when she got hacked. Someone changed her bio and had been tweeting at the same time she was tweeting. So Chalene changed her password to something out of the ordinary, logged back in and changed her bio.
Then, it happened again. The hackers were sending out porn and tweeting other people at the same time Chalene was on Twitter. Her other accounts were hacked as well. She felt like she wasn't safe in her own home. Even though it was an Internet attack and there wasn't a physical threat, Chalene recalls that it felt like it.
Darren shares where he was on the night of Chalene's cyberattack. He and his wife just got home from dinner and were flipping through Instagram when they noticed that Chalene's account had content she normally wouldn't post. So he texted her and said he thought she'd been hacked. She wrote back that she knew and was freaking out. He said to call him so they could get it under control and get the hackers out of her system.
3 Days of World-Class Training—Zero Travel!

Couldn't make it to Social Media Marketing World and AI Business World this year? Get all of the great content at a fraction of the price with a Virtual ticket.
That’s full access to recordings of every keynote, workshop, and session—the ones people travel thousands of miles to see. Don't wait. Get your Virtual ticket and enjoy actionable content that you can watch anytime, anywhere.
By the time Chalene called Darren, her Twitter, Instagram and Facebook had been taken over. And, though she didn't realize it yet, the hackers were also in her inbox.

Chalene and Darren spent eight hours, working through the night, trying to patch everything up.
People assume it's personal, Chalene says, but that's not the case. It hit her especially hard because social media is her livelihood. The hackers deleted everything she posted on Instagram over the last four and a half years, and they started posting videos of animal cruelty and violent porn. Chalene felt helpless and responsible. The cost of the hack, which included security experts, loss of wages and rebuilding her security, was in excess of $200,000.
Darren says hacking is a sport for some people and a hobby for others. They are experts in their field. Since they don't have legal ways to demonstrate their expertise, this is how they do it.
Don't worry about hackers, Darren suggests. Focus on what you need to do to protect yourself. Situations like this expose holes that we knew existed, and that we should have patched, but kept putting it off. It's like waiting until a health condition pops up and then deciding to get in shape. Sometimes it takes an unfortunate disaster to get someone to appreciate the value of simple preventive measures.
Listen to the show to hear how engaging with the hackers made things worse for Chalene.
What defenses to put in place
Darren says to protect yourself, you need to build a solid foundation for security. Get a password manager, such as 1Password, LastPass or Dashlane, and use it to generate strong passwords. Darren uses and recommends 1Password.

Chalene explains how the hackers got into her account. They called her email provider, said they were working on her behalf as security experts and needed to reset her password. Whoever they interacted with said they needed answers to her security questions. Common security questions, such as the street someone grew up on and the wife's maiden name, are easy to find online. And that's all someone needs to reset your email password.
Never answer security questions honestly, Darren suggests. You can go to all this work to come up with complex passwords, but if you answer security questions honestly, all somebody has to do is find and plug that information in. Once they have access to that email, every service that's connected to it is potentially at risk.
Listen to the show to discover which password manager we use for Social Media Examiner and why we love it.
How Gmail ensures security
Gmail offers 2-Step Verification, which is also known as 2-factor authentication.
After you enter your email and password, Gmail prompts you for a code. The code can either be sent to a mobile device or generated inside of an app like Google Authenticator or within 1Password. It expires, so you have to enter it within a certain amount of time. This process ensures that if someone else tries to access your account, or if you log in from a new browser or device, a code is needed to get into it.
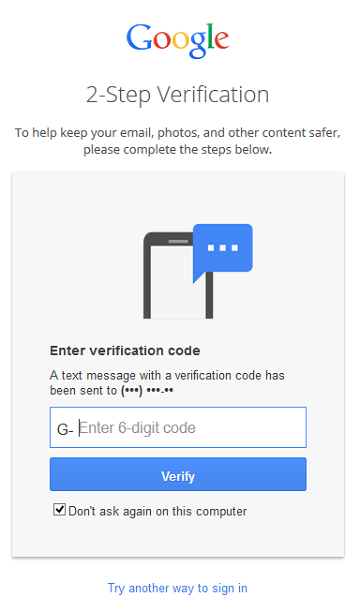
To set up password verification in Google Authenticator, open the app and click on the + sign that says “add one-time password.” It will show you a QR code. Take a picture of that with your phone. It plugs it in and will remember it from that moment forward.
A master password database, like 1Password, is extremely difficult for someone to crack, because of the level of encryption. The master password needs to be very strong but still memorable enough to enter frequently. If you use a weak master password, you open yourself up to threats. But if you make it so hard you forget your master password, you will not get into your vault, and will have to start over.
Listen to the show to hear where to store a copy of your master password for your password manager.
Securing Social Networks
Social networks offer their own version of security, Darren explains. For example, Facebook has a Code Generator for the mobile app that accomplishes the same thing as Gmail. You can use that alone or in tandem with 1Password or Google Authenticator.
Chalene shares how, after the hack, she had to change the online behaviors of everyone in her office. She used to share her accounts with assistants, but now everyone needs his or her own administrative privileges and 2-factor authentication on all sites and networks.

Chalene talks about the people who reached out to her after she shared her ordeal, who relayed their own experiences. People have said that even though they had 2-Step Verification, they still got hacked, because they clicked suspicious emails that asked them to verify their identity.
The U.S. Navy captures 110,000 cyberattacks every single hour, Darren explains. That's approximately 30 every second.
“These hackers and phishermen are only as capable as the amount of line we give them,” Darren elaborates. “I am shocked at how much information we willingly divulge.”
For example, he was at a food truck recently and noticed a clipboard with a sign-up form for their email list sitting out. He says he could have taken a picture of that list and had everybody's name, address, phone number and email address.
Email is another thing. We communicate primarily over plain text email, and those messages circulate. If somebody at work emails asking for someone's account number or an email password, and you reply, that's plain text that hasn't been encrypted. Eventually somebody can potentially get that.
While there are web password security options like One-Time Secret, Darren prefers users try alternatives for communicating sensitive information.
If you have an iOS device, turn on iMessaging. If you're an Android user, there's WhatsApp, which is cross-platform. There's also Hushmail, which has encrypted, paid options for individuals and businesses.
If you're going to send sensitive info, do it securely. Don't send it over a text message.
Listen to the show to learn why you should enable SMS notifications for security.
Want to Unlock AI Marketing Breakthroughs?
If you’re like most of us, you are trying to figure out how to use AI in your marketing. Here's the solution: The AI Business Society—from your friends at Social Media Examiner.The AI Business Society is the place to discover how to apply AI in your work. When you join, you'll boost your productivity, unlock your creativity, and make connections with other marketers on a similar journey.
I'M READY TO BECOME AN AI-POWERED MARKETERWhat Chalene did to move forward after the hack
It took three weeks from the initial hack for Chalene to make sure she was as safe as possible.
She took out a piece of paper and created a massive brainstorming list of every account, email and online membership site. Then she went through her spam folders and membership sites and old emails to find everything else she needed to secure post-crisis.
Chalene also added looking into what's going on with cybersecurity to her daily to-dos.
Listen to the show to hear Chalene compare her experience to being in a horror movie.
Web browsers, social logins and safety
While saving logins to web browsers is very convenient, it's only as safe as the steps you took to secure it, Darren says. For instance, if you use Safari and have a weak iCloud password, your information is not as safe.
However, browser extensions of password managers like 1Password are safe. Plus, you no longer have to save information in browsers. Go into Preferences, and turn off save passwords, personal information and autofill forms. To find it in Chrome, go into the Advanced Settings in Preferences.
Next, install the password manager browser extension. It will do the same thing saving passwords in the browser, but it'll do it more securely. You can save credit cards, all of your identities and every login you ever created.

The security extensions are much safer because the information from browsers can be captured. Whenever you go to a site and it plugs in your information, if someone were to spoof that site, it has your information.
Plus, if you have given login permissions to social logins, immediately go into the privacy settings of those apps and revoke access. You do not want to share accounts with other people or use one account, such as Facebook, to log into multiple sites. If someone penetrates Facebook, they have access to all of the sites that you connected to it.
Create an individual login for every account you have. Use your primary email address, secured with 2-factor authentication. You can also use aliases, a nice feature built into Gmail and Google apps.
Let's say your email address is [email protected] and you're enrolling for a service like Dropbox. Use [email protected], and it will forward any messages to your Gmail address. Anything you put after the + sign will end up in your inbox.
This allows you to identify which places are compromising your email address, which you can't do with a regular primary account. When you discover an issue or start getting a lot of spam, add a filter to the alias, delete the messages and start over with a new email address.
Listen to the show to hear some of my encounters with security issues.
Protecting yourself on the Cloud
You do need to worry about the Cloud, Darren says. Just last year, 47% of adults had their information exposed in one form or another. That's basically half the population.
To protect yourself when using Cloud programs like Dropbox and Evernote, use 2-Step Verification.
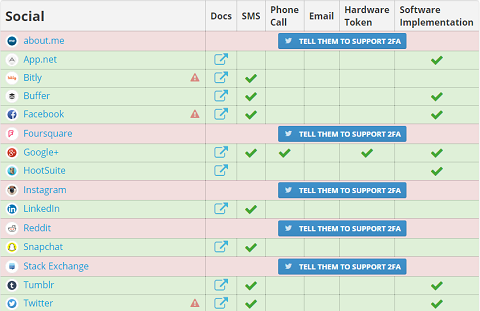
Two Factor Auth has a list of sites that do and do not offer 2-factor authentication. Darren recommends setting aside a couple of hours to protect all of your accounts. That way, if somebody tries to get into one of them, you'll get an alert.
If you don't want to give out your phone number, create a free number on Google Voice that you can forward to any other device. You receive text messages, plus Google Voice transcribes your voicemail messages for you. You can also classify messages as spam.
Listen to the show to learn more about TwoFactorAuth.org.
Why everyone should be concerned about security
Chalene believes a security hack is something everyone should anticipate could happen to them. You hear about people of notoriety, because they have a platform.
“I am fortunate enough be able to use what happened to me as an opportunity to help others,” Chalene says. “Someone taking over my social media account is not the end of the world. Having someone go into my bank account without my knowing could be devastating. Everyone needs to take the necessary precautions to avoid it.”
At first security seems overwhelming, but you just need to go through everything in the right order step-by-step to learn more, develop an expertise and be able to help others.
Darren says his website, BeyondthePassword.com is the security equivalent of Social Media Examiner. Once on there, download Darren's cybersecurity checklist: the 10 steps to protect yourself from hackers and stay safe online.
Listen to the show to hear more ways Beyond the Password can help.
Other Show Mentions
 Today’s show is sponsored by Social Media Success Summit 2015.
Today’s show is sponsored by Social Media Success Summit 2015.
Want to improve your social media marketing? Need to prove your efforts are working? Join 4,000 fellow marketers at the online mega-conference, designed to inspire and empower you.
Discover the best and newest ways to market your business on Facebook, LinkedIn, Twitter, Google+, YouTube, Instagram and Pinterest. Find new ways to improve your content and measure your results all from the comfort of your home or office. You'll be led by dozens of top social media pros, including Mari Smith, Mark Schaefer, Amy Porterfield, Christopher Penn and Michael Stelzner. Register now for Social Media Success Summit. Discount tickets are limited.
Social Media Success Summit is an online conference. It's 36 different sessions spread across 4 weeks. There are three sessions per day, three times per week, over four weeks. And it's on every conceivable social media platform you can imagine. Check it out. Visit SMSS15.com for significant early bird discounts.
Listen to the show!
.
Key takeaways mentioned in this episode:
- Connect with Chalene on her website.
- Listen to Chalene's five-part podcast on online security.
- Read Chalene's book Push and follow Chalene on Instagram and Facebook.
- Get your security checklist on Darren's site Beyond the Password.
- Follow Darren on Facebook and Instagram.
- Get a password manager like 1Password, LastPass or Dashlane.
- Check out Gmail's 2-Step Verification, Google Authenticator and Facebook Code Generator.
- Learn more about One-Time Secret.
- For secure messages, use iMessaging, WhatsApp and Hushmail.
- See which websites offer 2-factor authentication.
- Get an account on Google Voice.
- Learn more about the 2015 Social Media Success Summit.
- Read the 2015 Social Media Marketing Industry Report.
Help Us Spread the Word!
Please let your Twitter followers know about this podcast. Simply click here now to post a tweet.
If you enjoyed this episode of the Social Media Marketing podcast, please head over to iTunes, leave a rating, write a review and subscribe. And if you listen on Stitcher, please click here to rate and review this show.

Ways to subscribe to the Social Media Marketing podcast:
- Click here to subscribe via iTunes.
- Click here to subscribe via RSS (non-iTunes feed).
- You can also subscribe via Stitcher
How to Subscribe to this Podcast on an iPhone
Watch this quick video to learn how to subscribe on your iPhone:
[vimeo clip_id="116089190" width="230" height="408"].
What do you think? What are your thoughts on online security for business? Please leave your comments below.
Hacked photo, Verification photo and Security photo from Shutterstock.
Curious About How to Use AI?
Our newest show, AI Explored, might be just what you're looking for. It's for marketers, creators, and entrepreneurs who want to understand how to use AI in their business.
It's hosted by Michael Stelzner and explores this exciting new frontier in easy-to-understand terms.
Pull up your favorite podcast app and search for AI Explored. Or click the button below for more information.