Do you rely on your computer for business?
Is your computer and data secure?
To learn more about ways to protect yourself and your business, this episode of the Social Media Marketing podcast gives you insight into the subject.
More About This Show

The Social Media Marketing podcast is a show from Social Media Examiner.
It's designed to help busy marketers and business owners discover what works with social media marketing.
The show format is on-demand talk radio (also known as podcasting).
In this episode, you'll learn different ways to protect your data and make sure your business is back up and running very quickly if you were ever to lose it.
Share your feedback, read the show notes and get the links mentioned in this episode below!
Listen Now
Where to subscribe: Apple Podcasts | Spotify | YouTube Music | YouTube | Amazon Music | RSS
Here are some of the things you'll discover in this show:
Computer Security
Why secure your computer?
There are two main reasons to secure your computer.
Get World-Class Marketing Training — All Year Long!
Are you facing doubt, uncertainty, or overwhelm? The Social Media Marketing Society can help.
Each month, you’ll receive training from trusted marketing experts, covering everything from AI to organic social marketing. When you join, you’ll also get immediate access to:
- A library of 100+ marketing trainings
- A community of like-minded marketers
- Monthly online community meetups
- Relevant news and trends updates
- Peace of mind. If your hard drive was to crash or you had your computer stolen, you need to know that it doesn't spell the end of your business. It allows you to sleep at night. Theft and a hard drive crash are almost the same outcomes. Peace of mind is a big deal.
- Business continuity. You don't want the loss of your computer to be the end to their business. This is why it's essential to implement security measures. The good news about a lot of this stuff is, it's set and forget. It only takes a small amount of your time, and in certain cases some financial investment, to know that you will be able to continue to operate no matter what happens to your computer.
Recently I received a phone call from my office informing me that my two iMacs had been stolen.

When the police arrived we were informed that another office within the same building had also been targeted.
The alarm system was set, it hadn't been disarmed and even the motion sensors hadn't been triggered. They broke through the office window, taking the computers with them.
You'll hear the reason why my office was vulnerable.

In total I lost about a day and a half of my time and you'll discover how I got back online within 5 hours.
I thought I would share my story with you and hopefully you'll be able to take some notes from it.
Here are 9 tips to protect yourself from losing your data.
#1: Set-up a remote backup
I highly recommend that you have a remote back-up plan in place. I use CrashPlan and for approximately $60 a year have unlimited back-up capabilities.

Listen to the show to hear how CrashPlan works and the different account levels they offer.
#2: Back-up to an external hard drive
You have to make sure that your hard drive is external from your computer. If you put yourself in the minds of the thief, they want to make a quick buck. They don't really care about your hard drive, just your computer.
An external hard drive is critical. In my case they left the hard drive behind and I was able to plug it into my new computer. It was the key to everything.

For the iMac they have got a really cool thing called Time Machine.
Make sure you store your external hard drive somewhere out of sight. Remember the thieves unplug all the cables and just take the computer.
Listen to the show to hear how Time Machine works similar to CrashPlan, and how it can get you back up and running very quickly.
#3: Secure your browser passwords
You should make sure you have a password to log onto your computer. A password can be a deterrent, although when someone does steal your computer, they are likely to reformat the hard drive, rather than try to figure out the password.
Make sure you also password protect your web browser. This is really important because we access our banking accounts, merchant systems, blogging tools, email etc from within a web browser.
Everything seems to live out in the cloud these days. So it's critical to have that web browser protected. When it comes to setting up a master password, you'll learn about what Firefox offers differently to Chrome and Safari.
Listen to the show to hear why it's even more important to secure your web browser when working on a laptop.
#4: Use 1Password with Dropbox
You can buy 1Password on your android, your iPhone, tablet or any of your personal computers.
I have 1Password installed on my laptop, desktops, iPhone and iPad and what's really cool about it is that it integrates with Dropbox.
You'll discover how 1Password integrates with your web browser and synchronizes all your passwords. It's available on any of your devices, wherever you go, whenever you go.
The ability to have central storage that's encrypted and stored within Dropbox and accessible through 1PassWord, makes it easy for me to operate. It's the secret to everything.
Listen to the show to find out why you need to have strong passwords on both your Dropbox and 1Password accounts.
#5: Keep your blinds closed
I know this sounds crazy, but keeping your blinds closed is essential.
The bottom line is if I'd have had my blinds closed, the thieves wouldn't have been able to look in with a flashlight and see my computers. If it's out of sight, it's out of mind to a thief.
It seems so simple, but it's the easiest thing that we can do to protect ourselves.
Listen to the show to hear the advice given to me by the Police Department.
#6: Use a device location tool
LoJack is a tool that you can buy for Mac or PC. It allows you to report to the police that your computer has been stolen, and to track its location.
Discover Proven Marketing Strategies and Tips
Want to go even deeper with your marketing? Check out the Social Media Marketing Podcast! Publishing weekly since 2012, the Social Media Marketing Podcast helps you navigate the constantly changing marketing jungle, with expert interviews from marketing pros.
But don’t let the name fool you. This show is about a lot more than just social media marketing. With over 600 episodes and millions of downloads each year, this show has been a trusted source for marketers for well over a decade.
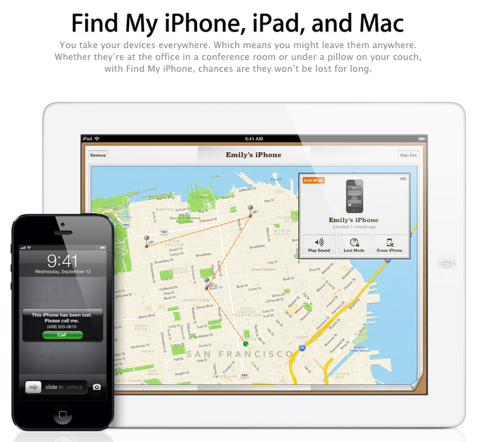
If you're a Mac user, there is a really cool feature called FindMyMac. If you enable the location device on all of your devices, you can log into iCloud and it will pull up a map and show you where your devices are.
Another piece of software called LogMeIn, is remote access software. I have it installed on my computer and if anyone does figure out how to hack into it, I can remotely log in from anywhere in the world to my computer and I try to look up the IP address to see where it is.
Listen to the show to discover how this feature can help you find your device and hopefully lead to recovery.
#7: Take photographs of serial numbers
Fortunately I still have the box from one of my iMacs because it was only 60 days old.
I recommend you take a photograph of the serial number on the box and store it somewhere safe. It can be really helpful to the police and pawn shops.
Listen to the show to find out the best places to store your serial numbers.
#8: Secure your office with motion sensors and video surveillance
If you have a home office or are in a physical building, you can secure your office a few different ways.
First and foremost, you should definitely have a security system. We have motion sensors and door sensors.
Motion sensors have a wide range of motion, so make sure the light comes on where your computer equipment is situated.
You'll learn about glass break detectors and how they work.
Video surveillance is another great option. There are a lot of cool things you can do with video surveillance and it's a lot cheaper than you think. Not only is it a good idea to install video surveillance on the outside of your building at points of entry, but also to have it installed in your office.
The equipment available today has improved a lot and Amazon have a really cool system called SVAT-CV301 that has day and night vision with high definition.
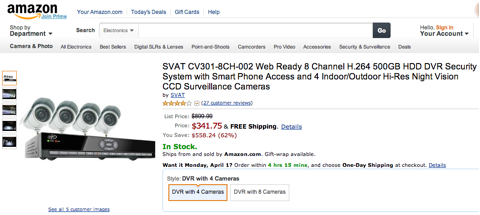
Listen to the show to hear how this device works and how it can lead to the capture of the culprit.
#9: Other steps to take
First of all make sure you have good insurance. A lot of insurance companies have riders that you can put on your policy that covers computer devices.
You'll find out about the experience I had with my insurance company, what you need to provide them with and the words to use to accelerate your claim.
When it comes to software, make sure you keep all the serial numbers. This is critical if your back-ups go bad. If you download your software through Amazon, they actually store all the serial numbers.
Listen to the show for more useful tips.
Something is Coming Soon …
If you listened to our last episode, I hinted about Project Torch. Listen to the show to find out more about Project Torch: My Kids Adventures.
My Kids Adventures is a movement for parents who want to bring adventure back to the family. It's going to be a great resource to help any parents or grandparents respond to children who say, “I'm bored, I don't know what to do.”

It will be a free online magazine for parents to help them create memorable adventures anywhere, whether it's inside or outside the home.
My Kids Adventures is in the development stage right now. Here are two things you can do if you want to help, or be a part of it.
- Get on the Founders list. The Founders list is a place where you can get the inside scoop on what's going on with My Kids Adventures. You can get on that list by going to My Kids Adventures.
- Join the movement. If you want to help us create content, or in any other way, visit My Kids Adventures or email us at [email protected].
I am extremely excited. This is a passion project for me and I'm fully committed to making this a success. I really do believe that we're going to change the lives of a lot of families as a result of this effort.
Please check out the cool video. Let your friends know about it. The launch date hasn't officially been released yet, so listen for more information in future podcasts.
Key takeaways mentioned in this episode:
- Check out CrashPlan for remote back-up.
- Take a look at Time Machine.
- Check out the 3 different web browsers: Firefox, Chrome and Safari.
- Find out more about 1Password and Dropbox.
- Learn about LoJack, FindMyMac and LogMeIn for device locators.
- Take a look at SVAT-CV301, video surveillance equipment.
- Check out Amazon for software downloads.
- Call in and leave your social media–related questions for us and we may include them in a future show.
- Learn more about My Kids Adventures.
Help Us Spread the Word!
Please let your Twitter followers know about this podcast. Simply click here now to post a tweet.
If you enjoyed this episode of the Social Media Marketing podcast, please head over to iTunes, leave a rating, write a review and subscribe.
Ways to subscribe to the Social Media Marketing podcast:
- Click here to subscribe via iTunes.
- Click here to subscribe via RSS (non-iTunes feed).
- You can also subscribe via Stitcher.
What do you think? What are your thoughts on protecting your data? Please leave your comments below.
Attention Agency Owners, Brand Marketers, and Consultants

Introducing the Marketing Agency Show–our newest podcast designed to explore the struggles of agency marketers.
Join show host and agency owner, Brooke Sellas, as she interviews agency marketers and digs deep into their biggest challenges. Explore topics like navigating rough economic times, leveraging AI, service diversification, client acquisition, and much more.
Just pull up your favorite podcast app, search for Marketing Agency Show and start listening. Or click the button below for more information.